OUR BLOG
Review Our Extensive Blog Library
Cloud Security Automation for Businesses
Moving your data and daily operations to the cloud offers excellent flexibility, but it also changes how you need to protect your network. Manual security checks and manual...
Cloud Security Risk Assessment Guide
Moving data and applications to the cloud is a standard practice for modern operations. However, simply hosting your files with a major provider does not guarantee their...
How Secure Is Cloud Computing?
Technology continues to change, along with the ways it is delivered to businesses. Since 1980, CTS Companies has maintained a single commitment: to help you figure out...
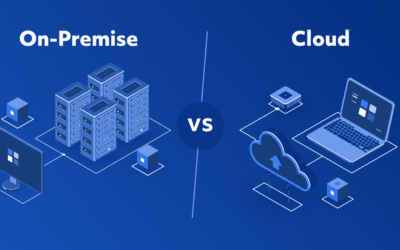
Cloud vs On-Premise Security: Which Is Safer?
Business leaders frequently ask us: is cloud more secure than on premise? It is a practical question that impacts your budget, your daily operations, and the safety of your...
Cloud Security Benefits for Businesses
Technology delivery methods change constantly, but our commitment at CTS Companies has remained the same since 1980: we help you figure out which technology you need to...
Cloud Security Risks Businesses Should Know
Moving your business operations to the cloud offers flexibility, scalability, and predictable costs. However, it also introduces new vulnerabilities. Many business owners...
12 Questions to Ask After Your MSP Is Acquired
A quick reality check When an MSP gets acquired, the logo may stay the same, but the incentives often change. If your IT provider has been acquired, the best way to protect...
How to Improve Cloud Security
Moving your daily operations and data to the cloud offers distinct advantages for your business. It allows your team to work from anywhere, collaborate easily, and scale...
How to Secure Cloud Infrastructure
Moving your data and daily operations to the cloud offers convenience and flexibility. But with that shift comes a critical responsibility: knowing exactly how to secure...
How to Secure Data in the Cloud
Moving business operations online is standard practice today. However, many IT managers and business owners still struggle with how to secure data in the cloud. Since 1980,...
How to Secure Sensitive Data in the Cloud
Moving operations to the cloud offers flexibility and efficiency that traditional on-premise servers simply cannot match. However, this shift changes how businesses must...
How to Build a Cloud Security Strategy
Since 1980, technology has changed dramatically. We have moved from heavy on-premise hardware to a world dominated by connectivity and remote access. However, at CTS...
How to Conduct a Cloud Security Assessment
Technology changes rapidly. Since 1980, CTS Companies has seen the landscape shift from mainframe terminals to on-premise servers, and now, to the cloud. While the way we...
Who Is Responsible for Cloud Security?
Moving your business operations to the cloud offers flexibility, scalability, and efficiency. However, it also introduces a dangerous misconception. Many business owners...
Cloud Security for Growing Businesses
Moving your operations to the cloud offers flexibility and speed, but it also introduces new questions about safety. Since 1980, CTS Companies has helped businesses figure...
How to Evaluate Cloud Provider Security
Technology changes rapidly. How businesses deliver their services changes even faster. However, since 1980, the commitment at CTS Companies has remained the same: helping...
Requesting Cybersecurity Service Quotes: Business Guide
Protecting your business data is no longer an optional line item; it is a fundamental requirement for staying in business. As threats evolve, so must your defense...
Cybersecurity Threat Detection and Response Services
Business owners and IT managers today face a difficult reality. The tools that protected companies five years ago are often insufficient against modern attacks. A simple...